Suspected China-linked Hackers Target Southeast Asian Militaries
Palo Alto Networks Unit 42 says a suspected China-based espionage group has been targeting military organizations in Southeast Asia using custom malware named AppleChris and MemFun, with activity dating back to at least 2020.
Unit 42 tracks the operation under the label CL-STA-1087, where STA stands for state-backed motivation. “The activity demonstrated strategic operational patience and a focus on highly targeted intelligence collection, rather than bulk data theft,” security researchers Lior Rochberger and Yoav Zemah said. They added that the attackers searched for files on military capabilities, organizational structures, and cooperation with Western armed forces.
According to Unit 42, the campaign shows classic advanced persistent threat behavior: carefully crafted delivery methods, defensive evasion techniques, stable infrastructure, and custom payloads designed to maintain long-term unauthorized access. The vendor tied several specific tools to the group, including the AppleChris and MemFun backdoors and a credential stealer called Getpass.
Unit 42 reported that the investigation began after analysts spotted suspicious PowerShell activity that put a script to sleep for hours and then established reverse shells to a command-and-control server. The exact way attackers first gained access to victim networks remains unknown, the company said.
AppleChris has been deployed in multiple variants across infected endpoints to maintain persistence and avoid signature detection. One delivery technique uses DLL hijacking. Once active, AppleChris connects to a C2 server and can list drives and directories, upload or download files, delete data, enumerate processes, run remote shells, and create hidden processes.
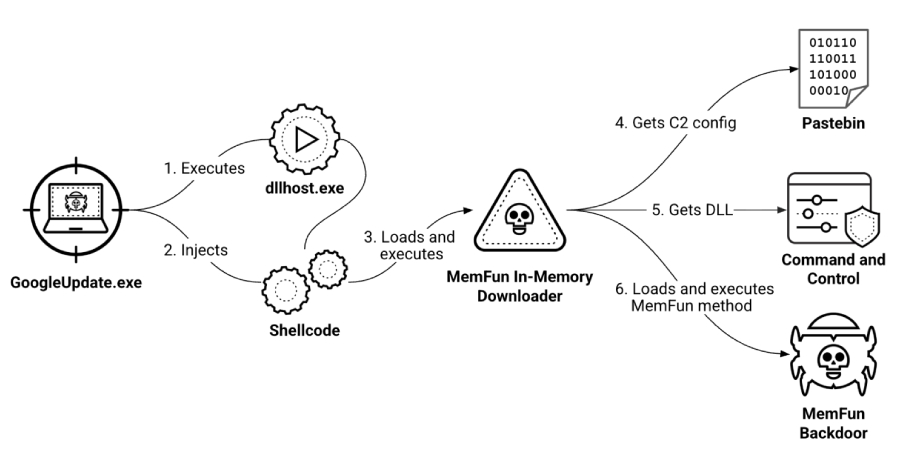
MemFun is built as a multi-stage, modular platform. Unit 42 described an initial loader that injects shellcode to run an in-memory downloader. That downloader pulls configuration data from Pastebin, contacts the C2 server, and retrieves a DLL that executes a backdoor payload. Because the DLL is fetched at runtime, operators can swap or update payloads without changing the on-disk components.
Both AppleChris and MemFun use Pastebin as a type of dead drop resolver: the malware reads a Pastebin entry, decodes a Base64 string, and obtains the actual C2 address. Unit 42 noted some AppleChris variants also use Dropbox to fetch C2 information, with Pastebin used as a fallback. The Pastebin entries linked to the campaign go back to September 2020.
To avoid automated defenses, Unit 42 said some strains include runtime sandbox evasion. “These variants trigger delayed execution through sleep timers of 30 seconds (EXE) and 120 seconds (DLL), effectively outlasting the typical monitoring windows of automated sandboxes,” the company said. Other techniques include process hollowing to run payloads inside legitimate Windows processes and timestomping to alter file timestamps.
Credential theft is also part of the toolkit. Unit 42 observed a custom Mimikatz build called Getpass that attempts to extract plaintext passwords, NTLM hashes, and other authentication material from lsass.exe memory to escalate privileges and move laterally.
Unit 42 concluded that the group demonstrated operational patience and careful operational security, keeping dormant access for months while conducting precise intelligence collection. Organizations in the region and partners should assume targeted espionage attempts continue and prioritize monitoring for the behaviors Unit 42 described.
For practical guidance on how organizations should prepare for and respond to targeted intrusions, see our step-by-step incident response guide.
#cybersecurity #espionage #military #malware #APT