Konni Uses KakaoTalk and Phishing to Spread EndRAT
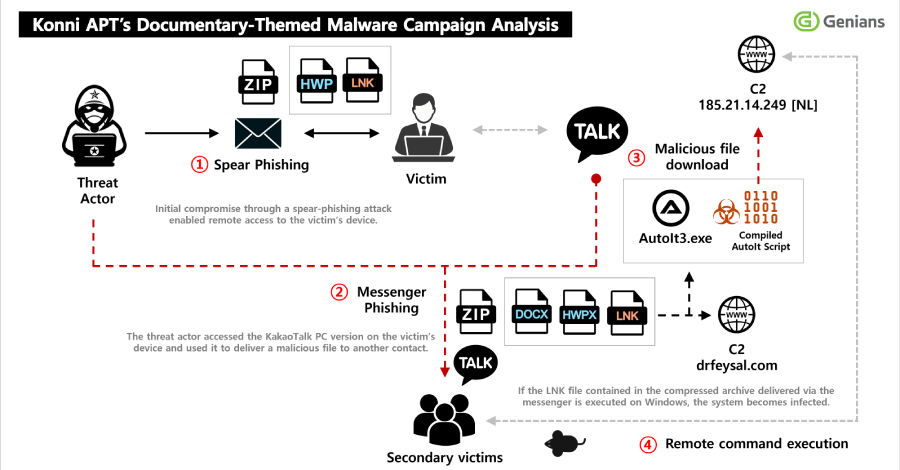
South Korean security firm Genians reported that North Korea-linked threat actors known as Konni used spear-phishing to install a remote access trojan (RAT) named EndRAT and then abused victims’ KakaoTalk desktop sessions to send malicious ZIP files to selected contacts.
Genians said initial access began with a spear-phishing email disguised as an appointment or notice. When recipients opened the attached ZIP and executed a Windows shortcut (LNK), the file downloaded a secondary payload, established persistence via scheduled tasks, and displayed a decoy PDF while the malware ran in the background.
According to the Genians Security Center, the downloaded RAT is written in AutoIt and dubbed EndRAT or EndClient RAT by researcher Ovi Liber. “This campaign is assessed as a multi-stage attack operation that extends beyond simple spear-phishing, combining long-term persistence, information theft, and account-based redistribution,” Genians said.
Genians found multiple malicious components on infected hosts, including AutoIt scripts for other RAT families such as RftRAT, Remcos RAT, and Quasar, suggesting the operators dropped several toolsets to improve resilience. “The threat actor stayed hidden in the compromised computer for over a year, spying via the webcam and operating the system when the user was absent,” Genians added.
One notable tactic in the campaign is turning compromised users into distribution points. Genians observed the attackers using a victim’s signed-in KakaoTalk desktop app to send a ZIP archive named to look like North Korea material. The ZIP contained an MSI installer (reported as “Stress Clear.msi”) that used a valid code signature from a Chinese company to appear legitimate, then launched scripts and an AutoIt loader on the host.
Beyond Windows targets, Genians also said the group targeted Android users and abused Google account credentials stolen from compromised PCs to access Google’s device management service, Find Hub, and remotely reset victims’ phones. “This attack did not exploit any security flaw in Android or Find Hub. The report indicates this targeted attack required PC malware to be present in order to steal Google account credentials and abuse legitimate functions in Find Hub,” a Google spokesperson told The Hacker News, while urging users to enable 2-Step Verification or enroll in the Advanced Protection Program.
Other recent research highlights parallel activity by different North Korea-linked groups. ENKI described an updated Comebacker variant used by the Lazarus Group against aerospace and defense targets, and Pulsedive reported a new JavaScript dropper used by Kimsuky. Both firms emphasized the use of tailored lures and multi-stage loaders in targeted espionage operations.
What to do: Genians and researchers recommend treating unexpected attachments with caution, enabling multi-factor authentication on important accounts, isolating and rebuilding affected machines if persistent access is suspected, and monitoring messaging apps for unusual outbound files. As Genians put it, the attack blends social engineering, long-term access, and account abuse to multiply its reach.
For practical guidance, see our guide on how to protect yourself from cyber attacks and learn what is cybercrime and how to protect yourself.
#Konni #KakaoTalk #EndRAT #Phishing #CyberAttack