DeepLoad Malware Campaign Uses ClickFix, WMI and APC Injection to Steal Credentials
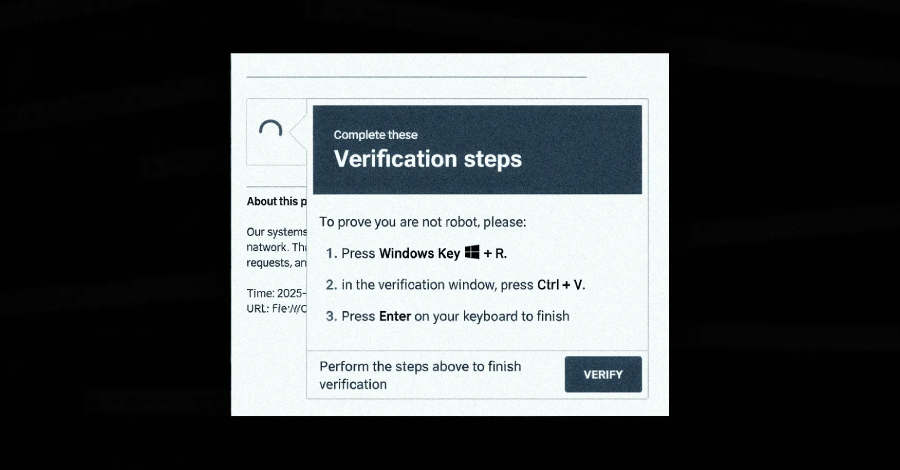
A new malware campaign is tricking users and stealing browser credentials, ReliaQuest said. The campaign uses ClickFix social engineering to get victims to run PowerShell commands. ReliaQuest researchers Thassanai McCabe and Andrew Currie reported the activity and shared technical details with The Hacker News.
The lure is simple and effective. Attackers ask users to paste a command into the Windows Run dialog under the pretext of fixing a bogus problem. ReliaQuest said the command launches mshta.exe, a legitimate Windows tool that downloads and runs an obfuscated PowerShell loader.
The loader hides its real work in meaningless variable assignments. ReliaQuest assessed that the padding is so large and consistent that the authors likely used an AI tool to assist in generating the obfuscation. “The sheer volume of padding likely rules out a human author,” ReliaQuest wrote. “If so, what once may have taken days to build could probably be produced in an afternoon.”
How DeepLoad hides
ReliaQuest said DeepLoad blends into normal Windows activity. The malware hides a payload inside an executable named LockAppHost.exe, which is associated with the Windows lock screen. That choice helps the code slip past many scans.
To avoid file-based detection, ReliaQuest explained, DeepLoad uses PowerShell’s Add-Type feature. The loader compiles C# code on the fly and writes a temporary DLL to the user’s Temp folder with a randomized name. That DLL changes every run, making name-based rules ineffective.
ReliaQuest also described an advanced in-memory trick. DeepLoad launches a trusted process in a suspended state, writes shellcode into its memory, and resumes the process. The team said the malware uses asynchronous procedure call injection, known as APC injection, so the main payload never appears decoded on disk.
Persistence and re‑infection
ReliaQuest warned that DeepLoad employs Windows Management Instrumentation to persist. The researchers said the malware creates a WMI event subscription that can re-run the attack three days after an apparent cleanup. “WMI served two purposes,” ReliaQuest wrote. “It broke the parent-child process chains most detection rules are built to catch, and it created a WMI event subscription that quietly re-executed the attack later.”
The team also found that the malware copies itself to removable media. Files that look like installers such as “ChromeSetup.lnk” and “Firefox Installer.lnk” are dropped onto USB drives. ReliaQuest said the goal is to trigger infections when a user double-clicks the shortcut on another machine.
Credential theft and browser hooks
ReliaQuest reported that DeepLoad immediately begins credential theft. The malware extracts stored browser passwords and session tokens. It also drops a malicious browser extension that intercepts credentials as users type them into login pages. The extension persists across sessions unless it is removed.
ReliaQuest emphasized the speed and stealth of these actions. “Credential theft starts immediately and captures passwords and sessions even if the primary loader is blocked,” the researchers said.
Related threats and wider context
G DATA detailed a separate but similar loader that uses Windows Internet Shortcut files in phishing emails. G DATA said that loader, called Kiss Loader, retrieves a secondary shortcut via WebDAV hosted on a TryCloudflare domain. The shortcut then runs scripts that download a Python-based loader and, in one case, deploy Venom RAT via APC injection.
ReliaQuest advised defenders to take concrete steps. The team recommended enabling PowerShell Script Block Logging and auditing WMI subscriptions on exposed hosts. They also suggested changing user passwords after an infection. “DeepLoad will adapt as defenders close gaps, so coverage needs to be behavior-based, durable, and built for fast iteration,” ReliaQuest wrote.
The disclosure shows how quick attackers are to combine social engineering, AI-assisted obfuscation, and native Windows features to stay under the radar. ReliaQuest and G DATA both urged organizations to focus on behavior-based monitoring and to assume attackers will keep innovating.
#DeepLoad #Malware #CredentialTheft #WMI #APCInjection #Cybersecurity