Critical EngageLab SDK Bug Put 50 Million Android Users and 30 Million Wallets at Risk
A widely used Android software development kit called EngageLab SDK contained a serious security flaw that could have exposed private data on millions of devices. The Microsoft Defender Security Research Team said the bug let apps on the same phone bypass Android’s security sandbox and access sensitive information without permission.
How the flaw worked
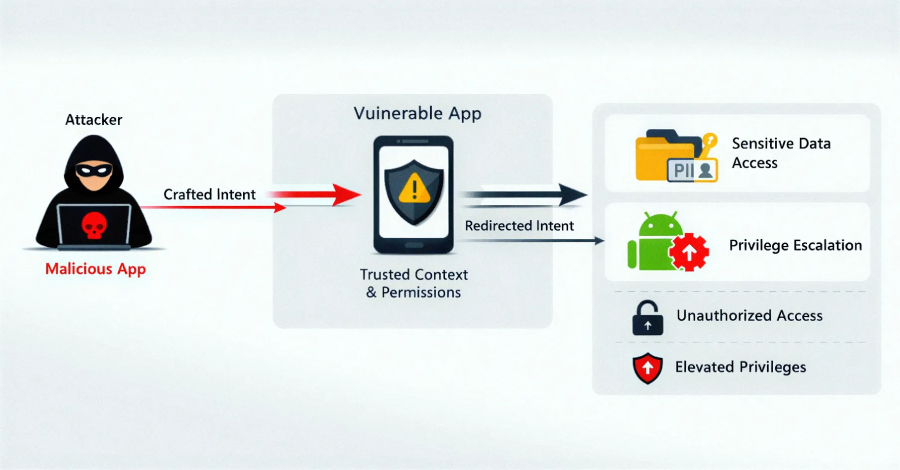
Microsoft identified the weakness as an intent redirection vulnerability in EngageLab SDK version 4.5.4. In Android, intents are messaging objects apps use to request actions from other app components. Microsoft explained that intent redirection happens when an app sends an intent from a trusted context and that intent is manipulated to gain access to protected components or data.
The practical risk was straightforward and urgent. Microsoft said a malicious app already installed on a device could exploit the SDK to read internal directories of other apps that had the SDK integrated into them. That scenario could expose private data stored by those apps. Microsoft also noted that the vulnerable SDK was integrated into many apps tied to cryptocurrency and digital wallets.
Scale and scope
Microsoft reported that the vulnerable wallet apps alone accounted for more than 30 million installations. When non-wallet apps using the same SDK are included, the total installs exceeded 50 million, Microsoft said. The company added that apps detected using the vulnerable SDK versions were removed from the Google Play Store following the investigation.
EngageLab released a patched SDK, version 5.2.1, after responsible disclosure. Microsoft said the disclosure began in April 2025 and the vendor published the fix in November 2025. Developers who still use older SDK builds are being urged to update immediately.
Was the flaw exploited?
Microsoft said there is no evidence the vulnerability was used in real-world attacks. Still, the company warned that even simple flaws in upstream libraries can cascade and affect millions of devices. “This case shows how weaknesses in third-party SDKs can have large-scale security implications, especially in high-value sectors like digital asset management,” Microsoft said.
What developers and users should do
- Update the SDK. Microsoft recommended that developers switch to EngageLab SDK version 5.2.1 or later.
- Limit exported components. Microsoft warned that integrations exposing exported components increase supply chain risk.
- Validate trust assumptions. Microsoft advised developers to avoid relying on implicit trust between app boundaries and to validate incoming intents.
These steps reflect the practical guidance Microsoft provided. The company emphasized that apps increasingly depend on third-party SDKs, creating opaque supply chain dependencies that can be abused if trust boundaries are not enforced.
Broader lessons
The EngageLab incident highlights a growing reality in mobile security. Third-party libraries speed development. They also expand the attack surface, Microsoft said. Security teams and app makers need to treat SDKs as first-class parts of their security programs, according to Microsoft.
Auditing dependencies, applying patches promptly, and limiting exported interfaces are low-cost measures that reduce risk. Microsoft pointed out that small flaws in widely distributed components can become large problems because of scale.
For users, the immediate advice is simple. Keep apps updated and prefer apps from vendors who publish clear security practices. For developers, prioritize dependency hygiene and test how third-party code interacts with app boundaries.
The EngageLab case serves as a reminder. Supply chain security is not abstract. It can reach into wallets and other high-value apps. Microsoft urged action and provided a concrete fix. Developers should follow that lead and patch vulnerable integrations now.
#AndroidSecurity #SDKVulnerability #SupplyChainRisk #CryptoSecurity #MobileSecurity #PatchNow