Microsoft Warns IRS Phishing Hits 29,000 Users With ScreenConnect Malware
Microsoft is warning that attackers are using the U.S. tax season to push phishing emails and malware at scale, with one campaign alone affecting more than 29,000 users across 10,000 organizations.
The Microsoft Threat Intelligence and Microsoft Defender Security Research teams said the messages are designed to look urgent and believable, often posing as refund notices, payroll forms, filing reminders, or requests from tax professionals.
How the Attack Works
That timing matters.
As Microsoft explained, many of these emails are built to catch people when they are expecting tax related messages and may act quickly without checking the details.
The company said some campaigns are aimed at everyday users looking for personal and financial information, while others specifically target accountants and other professionals who regularly handle sensitive documents and financial records.
Some of the attacks rely on phishing as a service platforms, which let criminals buy or rent ready made phishing kits.
Microsoft said one campaign used Certified Public Accountant themed lures to send victims to phishing pages linked to the Energy365 kit, which is estimated to send hundreds of thousands of malicious emails every day.
Another campaign used QR codes and W2 themed messages to target about 100 organizations, mainly in manufacturing, retail, and healthcare in the U.S., and directed victims to fake Microsoft 365 login pages built with the SneakyLog, also known as Kratos, platform to steal credentials and two factor authentication codes.
Other campaigns took a different route.
Microsoft said tax themed domains were used to trick users into clicking bogus links that led to the installation of legitimate remote monitoring and management software, including ConnectWise ScreenConnect, Datto, and SimpleHelp.
These tools are normally used by IT teams, but in the wrong hands they can give attackers persistent access to compromised devices, allowing them to steal data, harvest credentials, and move deeper into the network.
IRS and Crypto Lures
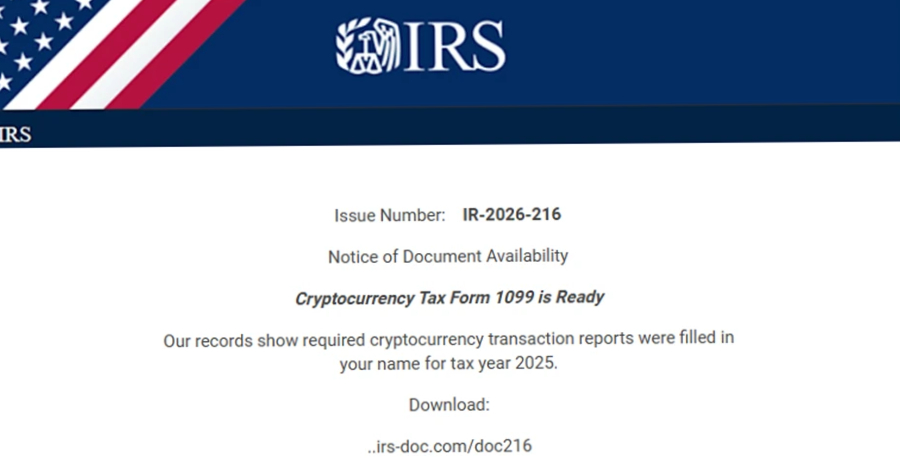
One campaign impersonated the Internal Revenue Service and used a cryptocurrency lure to target higher education organizations in the U.S.
Microsoft said the emails told recipients to download a fake Cryptocurrency Tax Form 1099 from domains such as irs-doc[.]com and gov-irs216[.]net, which ultimately delivered ScreenConnect or SimpleHelp.
In another case, attackers targeted accountants and related organizations with requests for help filing taxes, then used the malicious link to install Datto.
Large-Scale Phishing Operation
Microsoft also highlighted a large scale phishing operation it observed on February 10, 2026.
The company said more than 29,000 users across 10,000 organizations were affected, with about 95 percent of the targets located in the U.S.
The biggest industry groups included financial services at 19 percent, technology and software at 18 percent, and retail and consumer goods at 15 percent.
In that campaign, the emails pretended to be from the IRS and claimed that suspicious tax returns had been filed under the recipient’s Electronic Filing Identification Number, or EFIN.
Victims were told to review the returns by downloading a so called IRS Transcript Viewer.
Microsoft said the emails were sent through Amazon Simple Email Service, and the button inside them said Download IRS Transcript View 5.1.
Clicking it redirected users to smartvault[.]im, a domain that tried to look like SmartVault, a known document management and sharing service.
Microsoft said the phishing site used Cloudflare to block bots and automated scanners, which meant the main payload was only shown to real people.
That payload was a maliciously packaged version of ScreenConnect, which gave attackers remote access and helped them with follow on theft and exploitation.
What Microsoft Recommends
The tax themed wave is part of a wider rise in abuse of remote monitoring and management tools.
Huntress recently reported that RMM abuse has jumped 277 percent year over year.
Elastic Security Labs researchers Daniel Stepanic and Salim Bitam said these tools are often trusted because IT departments use them legitimately.
As they put it, organizations should stay vigilant and audit their environments for unauthorized RMM usage.
Microsoft recommends that organizations enforce two factor authentication for all users, apply conditional access policies, monitor incoming email and visited websites, and block access to known malicious domains.
The wider lesson is simple, according to the companies tracking these campaigns: if a tax message creates pressure to click, download, or log in immediately, it deserves extra scrutiny before anyone opens it.
#Cybersecurity #Phishing #Microsoft #RMM #ScreenConnect #IRS