Coruna iPhone Zero-Day Exploit Kit Reuses 2023 Triangulation Code
A powerful iPhone hacking toolkit known as Coruna is drawing fresh concern after researchers said it reuses exploit code linked to Apple attacks first seen in 2023. Kaspersky said the kernel exploit used in Coruna is an updated version of the same code involved in the Operation Triangulation campaign, a campaign that targeted iOS devices with zero-day bugs.
What Researchers Found
The new findings matter because Coruna is not just another isolated exploit.
Google and iVerify first documented the kit earlier this month, saying it can target iPhones running iOS 13.0 through 17.2.1.
In total, the toolkit includes five full iOS exploit chains and 23 exploits, including CVE-2023-32434 and CVE-2023-38606, both of which were used as zero-days in Operation Triangulation.
Boris Larin, principal security researcher at Kaspersky GReAT, said the public evidence was not enough at first to prove Coruna and Triangulation were tied together.
But he said the newer code shows clear continuity. “Coruna is not a patchwork of public exploits; it is a continuously maintained evolution of the original Operation Triangulation framework,” Larin told The Hacker News.
He added that checks for newer processors such as Apple’s M3 family show the codebase has been actively expanded.
According to Kaspersky, the kernel exploits in Coruna and Triangulation were written by the same author and built on the same exploitation framework.
The company said Coruna also adds four more kernel exploits and includes support for Apple’s A17, M3, M3 Pro and M3 Max chips.
Kaspersky also found checks for iOS 17.2 and for iOS 16.5 beta 4, the latter of which patched all four vulnerabilities used in Operation Triangulation.
How the Attack Works
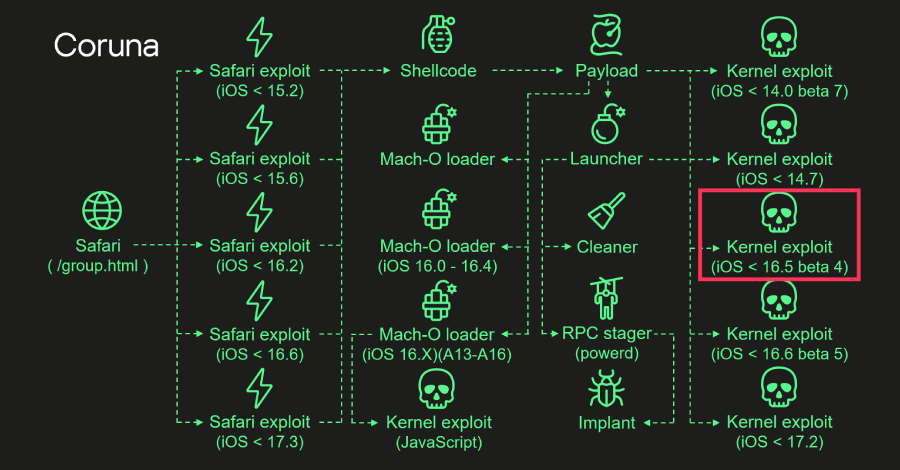
The attack flow is straightforward in concept, even if the code is highly advanced.
Kaspersky said the victim first visits a compromised website in Safari.
A stager then fingerprints the browser and operating system, chooses the right exploit, and delivers a payload that starts the kernel exploit.
Kaspersky said the payload then runs kernel exploits, Mach-O loaders, and the malware launcher.
That launcher coordinates post-exploitation steps, drops the final implant, and cleans up traces to make the intrusion harder to spot.
Where Coruna Has Been Seen
Google said Coruna has been seen in three different contexts, which makes the case especially unsettling.
The search company traced early activity to a “customer of a surveillance company” in February last year.
Five months later, Google said a more complete version appeared in an espionage campaign linked to a suspected Russia-aligned actor that hid the code in a visitor counter on Ukrainian websites.
Later, Google and iVerify saw it again in a profit-driven campaign using fake Chinese gambling and cryptocurrency sites to deliver the PlasmaLoader malware, also tracked as PLASMAGRID.
iVerify’s cofounder Rocky Cole said the code looks like a sophisticated toolkit that may have escaped its original environment.
“It’s highly sophisticated, took millions of dollars to develop, and it bears the hallmarks of other modules that have been publicly attributed to the US government,” Cole told WIRED.
He called Coruna “the first example” he has seen of likely US government tools being used by both adversaries and cybercriminal groups.
What Defenders Should Know
There are limits, however.
Google said Coruna is confirmed against iOS 13 through 17.2.1, and that Apple patched the exploited flaws in later iOS releases.
Google also said the toolkit checks whether Lockdown Mode is enabled and stops if it is.
Still, iVerify believes the campaign has already hit large numbers of devices.
Based on traffic seen to a command and control server used by the criminal version of the kit, the company estimated roughly 42,000 devices may have been compromised in that campaign alone.
iVerify chief product officer Spencer Parker said the underlying exploit framework is polished, while the malware added by criminals looks rougher.
“My God, these things are very professionally written,” Parker said of the exploit modules.
He said the extra payloads aimed at draining crypto wallets, stealing photos, and sometimes emails appear to have been bolted on later.
Why This Matters
For defenders, the big lesson is simple.
Even rare zero-day tools can spread far beyond their original purpose once they leak or get resold.
As Larin put it, “What began as a precision espionage tool is now deployed indiscriminately.”
With more exploit kits circulating and being reused, unpatched iPhones remain a valuable target for both spies and cybercriminals.
#iPhoneSecurity #ZeroDay #iOSExploit #CyberAttack #MobileSecurity #AppleSecurity