Mass DNS Hijacking by APT28 Targets SOHO Routers and Steals Tokens
A Russia-linked group known as APT28 has run a wide DNS hijacking and espionage campaign that abused insecure home and small office routers. Lumen’s Black Lotus Labs called the operation FrostArmada and Microsoft attributed the activity to APT28 and its subgroup tracked as Storm-2754.
What happened
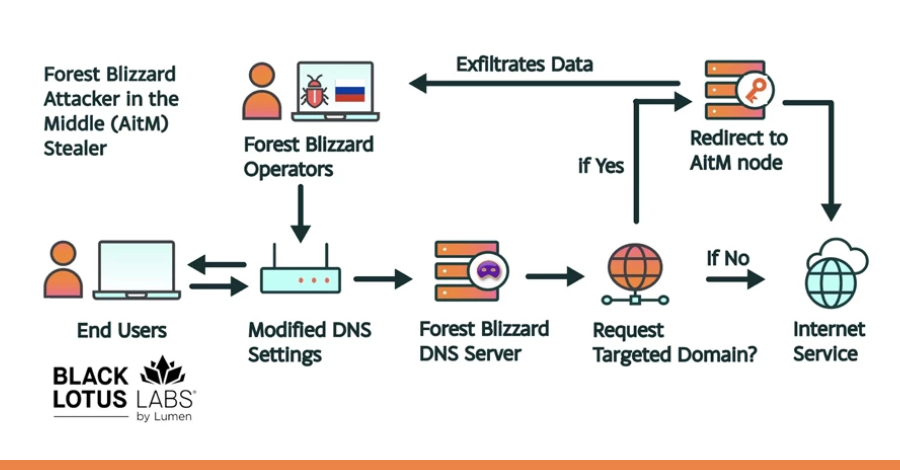
Attackers gained remote administrative access to MikroTik and TP-Link SOHO devices and changed their DNS settings to use resolvers the actors controlled. Black Lotus Labs said the reconfiguration caused DNS requests from entire local networks to be resolved by attacker-owned servers. Microsoft explained that this allowed the adversary to passively observe and redirect traffic without installing malware on endpoints.
The campaign began in a limited fashion around May 2025 and expanded in August, according to researchers at Lumen. At its peak in December 2025, Black Lotus Labs found more than 18,000 unique IP addresses across at least 120 countries communicating with the malicious infrastructure. Microsoft said it identified over 200 organizations and roughly 5,000 consumer devices impacted by the campaign.
How the attacks worked
At a technical level, the attackers used known vulnerabilities and default or weak device credentials to take control of routers. Microsoft and Black Lotus Labs reported that some TP-Link WR841N routers were likely exploited using CVE-2023-50224, an authentication bypass vulnerability that can expose stored credentials via crafted HTTP requests. Black Lotus Labs and Microsoft said the actors then set routers’ DNS to point to actor-controlled resolvers.
When a user requested an email login, a cloud service, or a webmail page, the malicious DNS resolver returned addresses that routed the connection through attacker infrastructure. There the adversary attempted adversary-in-the-middle (AiTM) operations on Transport Layer Security connections to harvest passwords, OAuth tokens, and other credentials. “Their technique modified DNS settings on compromised routers to hijack local network traffic to capture and exfiltrate authentication credentials,” Black Lotus Labs said.
Who was targeted
Microsoft and Lumen said the activity mainly targeted government institutions, including ministries of foreign affairs and law enforcement, along with third-party email and cloud providers. The U.K. National Cyber Security Centre assessed the operations as opportunistic. The NCSC said the actor gained visibility into a large pool of candidate users and then filtered down victims of higher intelligence value.
Microsoft noted that some of the intercepted domains were associated with Outlook on the web and that AiTM activity was observed against non-Microsoft hosted servers at several government organizations in Africa. “For nation-state actors like Forest Blizzard, DNS hijacking enables persistent, passive visibility and reconnaissance at scale,” Microsoft said.
Why this matters
The attack required no malware on user devices. Ryan English, a security engineer at Black Lotus Labs, told reporters that the group did not need to drop code on endpoints. “Everyone is looking for some sophisticated malware,” English said. “These actors did not use malware. They used classic, low-noise techniques that get the job done.”
Microsoft warned that while the observed use of AiTM in this campaign focused on collection, an attacker in that position could also deploy malware or cause denial of service. Black Lotus Labs engineer Danny Adamitis said the actor adapted quickly after public reporting, shifting from a targeted malware-based approach to broad DNS reconfiguration once the capability was available.
Disruption and response
The malicious infrastructure has been disrupted and taken offline through a joint operation involving the U.S. Department of Justice, the FBI, and international partners, Microsoft and Lumen said. Both vendors urged administrators and users to patch devices, change default credentials, and update firmware on SOHO routers. The U.K. NCSC published guidance on securing home and small office devices, the agency confirmed.
Network defenders should treat edge devices as high risk. Microsoft emphasized that compromising upstream devices gives attackers a stealthy path into larger enterprise environments. Black Lotus Labs recommended inventorying routers, applying vendor updates, and enforcing strong authentication on management interfaces.
Security teams and home users can reduce exposure by installing firmware updates, disabling remote administration, and using reputable DNS services. Microsoft and Lumen urged quick action given the scale and passive nature of the campaign. For more practical tips on staying safe online, check out our guide on how to protect yourself from cyber attacks.
#DNSHijacking #APT28 #SOHORouters #CyberEspionage #MikroTik #TPLink