APT37 Uses Facebook Friend Requests to Deliver RokRAT via Tampered PDF Viewer
North Korea-linked hackers are using Facebook friend requests to push a remote-access trojan known as RokRAT, researchers at the Genians Security Center said. The group, tracked as APT37, also known as ScarCruft, converted social trust into an infection channel.
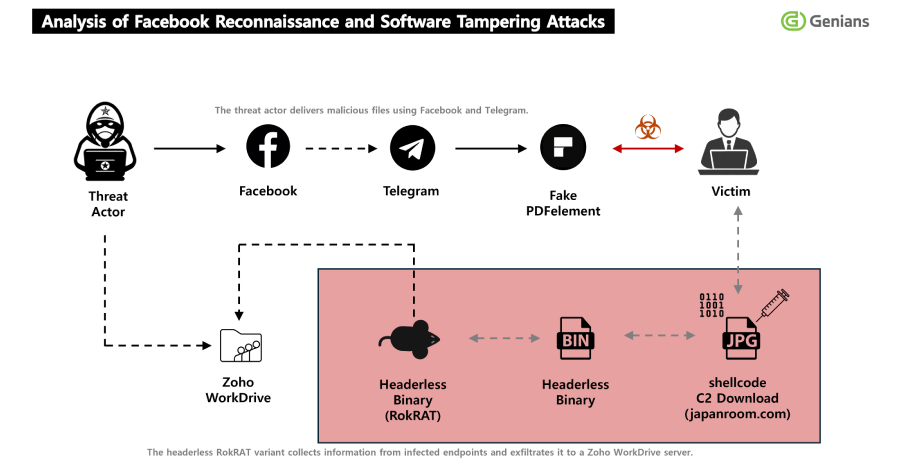
Genians Security Center, abbreviated as GSC, said the threat actor created two Facebook accounts with locations set to Pyongyang and Pyongsong. “The threat actor used two Facebook accounts with their location set to Pyongyang and Pyongsong, North Korea, to identify and screen targets,” GSC wrote. After friending targets, the actor moved conversations to Messenger and then to Telegram to deliver a malicious archive, the firm added.
How the trick works
The initial lure is social engineering, a tactic where attackers manipulate victims into divulging confidential information. GSC found the attackers posed as experts and used a fake need to view encrypted military-style documents. Victims were told they had to install a special PDF viewer to open files. The installer was a tampered build of Wondershare PDFelement. When launched, that program ran embedded shellcode and gave the attackers an initial foothold, GSC said.
From there, the tampered installer reached back to a command-and-control address listed as japanroom[.]com. GSC reported the next stage was delivered as a JPG named 1288247428101.jpg. That image carried the final RokRAT component. “This is assessed as a highly evasive strategy that combines legitimate software tampering, abuse of a legitimate website, and file extension masquerading,” GSC said.
RokRAT capabilities and infrastructure
Zscaler ThreatLabz previously documented RokRAT using cloud storage services as part of its command-and-control. Zscaler said in February 2026 that RokRAT variants have abused Zoho WorkDrive to host instructions and payloads during campaigns it labeled Ruby Jumper. Zscaler found that RokRAT can capture screenshots, run remote commands through cmd.exe, collect host information, and perform system reconnaissance. The tool also includes tactics to evade security programs such as Qihoo 360 Total Security, Zscaler noted.
GSC emphasized RokRAT’s stability of purpose. “Its core functionality has remained relatively stable and has been reused repeatedly across multiple operations over time,” the researchers said. The group has therefore focused on evolving delivery, execution, and evasion rather than rewriting the implant itself.
What defenders should do
- Verify contacts before installing software. GSC urges users to confirm unexpected friend requests and to avoid installing non-official builds of software.
- Block and monitor connections to suspicious domains. GSC named japanroom[.]com as an infrastructure element used in the chain.
- Harden email and messaging vectors. CYFIRMA and other threat intelligence teams recommend rules that flag archives containing executable installers and unusual file name patterns.
- Use vetted app sources. Prefer official vendor downloads and use endpoint controls that prevent unsigned installers from running.
- Keep detection tuned for shellcode loaders and image files that deviate from normal patterns. Zscaler highlighted the use of JPG files to hide payloads.
Cybersecurity firms stress that social engineering remains a primary attack path. GSC and Zscaler both show actors can chain simple trust-building into a complex multi-stage compromise, a concept detailed in the cyber-kill-chain model. Security teams should treat incoming social contacts with caution and enforce controls that limit user installation of unsigned tools.
The campaign illustrates a broader trend where state-linked groups reuse established implants and improve how they reach victims. GSC and Zscaler provide technical details that defenders can map to network and endpoint alerts. Organizations that manage sensitive national security or defense-related content should assume social platforms can be weaponized and plan accordingly.
#cybersecurity #APT37 #RokRAT #socialengineering #threatintel