Is AI Deployment Actually Delivering the ROI You Planned For?
A lot of companies went into AI deployment with real expectations. Faster workflows, lower costs, better decisions. And some of...
Explore practical cybersecurity guides covering cyber attacks, vulnerabilities, security best practices, and cyber awareness with real-world insights and easy explanations.
A lot of companies went into AI deployment with real expectations. Faster workflows, lower costs, better decisions. And some of...

Open any cybersecurity newsletter right now and you’ll almost certainly see the words “Mythos-ready.” Vendors are using it, consultants are...

Let me ask you something. When was the last time you actually read the privacy policy of an app before...

Learn what is phishing, how phishing attacks work, types of phishing scams, real-world examples, and proven strategies to protect yourself...

In today’s digital landscape, cybersecurity threats are evolving faster than ever. Organizations of all sizes struggle with how to protect...

On March 24, 2026, one of the most widely used AI gateway libraries got hit by a supply chain attack....

Anthropic introduced Model Context Protocol (MCP) in November 2024, and within months it became the hottest standard for connecting AI...

A few weeks ago, a colleague told me his father transferred ₹60,000 to a scammer. The scammer called pretending to...

Let me be real with you. When I first heard the term “vibe coding,” I thought it was a joke....

So, I did something a little unhinged last week. I set up an AI agent, gave it a set of...
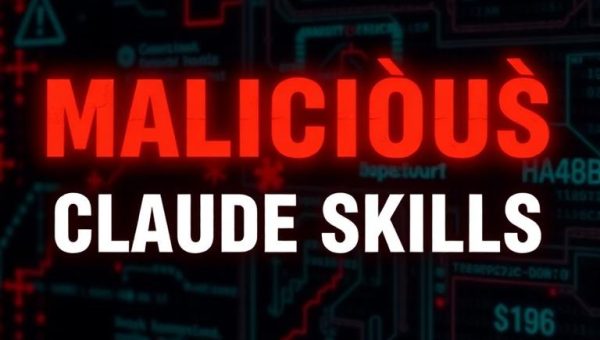
So I was going through my usual morning security feed when a headline stopped me cold. Straiker, a firm that...

Imagine you are working in the finance team. You get a video call from your CEO. The face matches. The...