North Korean Hackers Push 1,700 Supply Chain Malware Packages Across npm, PyPI, Go, Rust
Security firms have uncovered a large, coordinated campaign that slipped malicious code into open-source package registries. The activity is linked to a persistent North Korea-aligned group and spans npm, PyPI, Go, Rust, and Packagist. The effort is notable for scale and for how the malware hides inside apparently legitimate developer tooling.
What researchers found
Socket security researcher Kirill Boychenko said the campaign published packages that impersonated real developer libraries. “The threat actor’s packages were designed to impersonate legitimate developer tooling, while quietly functioning as malware loaders, extending Contagious Interview’s established playbook into a coordinated cross-ecosystem supply chain operation,” Boychenko said. Socket identified hundreds of malicious modules and traced specific packages across ecosystems.
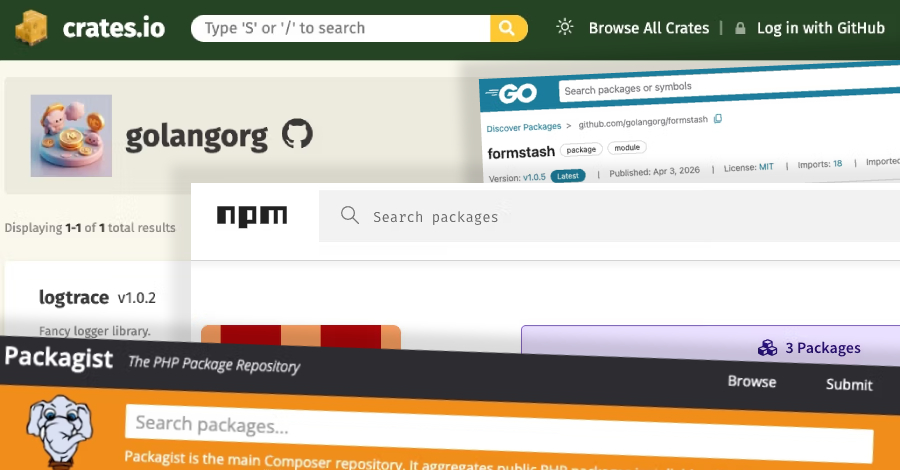
Researchers found malicious packages with names resembling logging and licensing helpers. Examples include npm modules such as dev-log-core, logger-base, logkitx, pino-debugger, debug-fmt, and debug-glitz. On PyPI, the packages included logutilkit, apachelicense, fluxhttp, and license-utils-kit. The Go and Rust entries included github[.]com/golangorg/formstash, github[.]com/aokisasakidev/mit-license-pkg, and logtrace. Packagist contained golangorg/logkit. Socket said these were part of a larger set.
How the malware works
The identified packages act as loaders. They fetch platform-specific second-stage payloads. Those payloads behave like infostealers and remote-access trojans. They gather data from web browsers, password managers, and cryptocurrency wallets. That makes them a high risk for developers and any system that builds from these dependencies.
Socket reported a Windows variant delivered via the PyPI package license-utils-kit. It described this as a “full post-compromise implant” capable of running shell commands, logging keystrokes, stealing browser data, uploading files, terminating browsers, deploying AnyDesk for remote access, creating an encrypted archive, and downloading additional modules. The breadth of functionality shows the campaign is not just about initial access. It includes deep post-compromise capabilities.
Stealthy placement and persistence
What made detection harder was how the malicious code was hidden. The payloads did not trigger during package installation. Instead, attackers embedded malicious calls inside functions that looked like normal behavior. In one case, the code was concealed in Logger::trace(i32). That kind of placement reduces developer suspicion and increases the chance the code runs in production environments.
Socket said the campaign expanded across five ecosystems and identified more than 1,700 malicious packages linked to the activity since January 2025. The cross-ecosystem spread is a sign of a well resourced supply chain operation that aims to turn open source modules into initial access paths for espionage or financial theft.
Wider context and social engineering
The discovery is part of a broader pattern tied to North Korean financially motivated actors. Previous incidents include the compromise of the Axios npm package to deliver an implant known as WAVESHAPER.V2 after a targeted social engineering attack on the maintainer. Analysis links the activity to a cluster tracked as UNC1069, which overlaps with tracked groups such as BlueNoroff and Stardust Chollima.
Security Alliance SEAL said it blocked 164 domains tied to UNC1069, impersonating services like Microsoft Teams and Zoom, between February 6 and April 7, 2026. SEAL warned the attackers use social engineering over Telegram, LinkedIn, and Slack, and often deliver fake meeting links that install malware. “UNC1069 operates multi-week, low-pressure social engineering campaigns across Telegram, LinkedIn, and Slack either impersonating known contacts or credible brands or by leveraging access to previously compromised company and individual accounts before delivering a fraudulent Zoom or Microsoft Teams meeting link,” SEAL said.
SEAL added a tactical note about patience. “Operators deliberately do not act immediately following initial access. The implant is left dormant or passive for a period following compromise,” the group observed. That delay helps the attacker remain unnoticed while maximizing data exfiltration.
Microsoft also weighed in. Sherrod DeGrippo, general manager for threat intelligence at Microsoft, said DPRK-linked actors continue to evolve their tools and infrastructure. “What we are seeing consistently is ongoing evolution in how DPRK linked, financially motivated actors operate, shifts in tooling, infrastructure, and targeting, but with clear continuity in behavior and intent,” DeGrippo said.
The takeaway is clear. Developers should assume dependencies can be targeted. Audit supply chain sources. Use dependency allow lists and reproducible builds. Monitor for unusual outbound connections from build systems. Small steps reduce the risk of a single malicious package leading to a major breach.
For developers looking to understand the fundamentals of open-source security, our guide on what is cyber security is a great starting point. To learn more about how to protect your projects from malicious dependencies, check out our how to protect yourself from cyber attacks in 10 easy steps guide.
#SupplyChain #Malware #OpenSourceSecurity #NorthKorea #DevSecOps #UNC1069